[WORKFLOW] npmjs publishing OIDC permission#2135
Conversation
Changelog ReminderReminder to update the CHANGELOG.md for any of the modified packages in this PR.
|
Codecov Report✅ All modified and coverable lines are covered by tests. 📢 Thoughts on this report? Let us know! |
0dff7ae to
445186b
Compare
| name: Upgrade ethereum-contracts on canary testnet (protocol release version "canary") | ||
|
|
||
| if: false # disable this for now | ||
|
|
||
| needs: [all-packages-tested] | ||
|
|
||
| runs-on: ubuntu-22.04 | ||
|
|
||
| strategy: | ||
| fail-fast: false | ||
| matrix: | ||
| network: [optimism-sepolia] | ||
|
|
||
| defaults: | ||
| run: | ||
| shell: nix develop .#ci-default -c bash -xe {0} | ||
|
|
||
| steps: | ||
| - uses: actions/checkout@v4 | ||
|
|
||
| - uses: DeterminateSystems/nix-installer-action@v13 | ||
|
|
||
| - name: Build | ||
| run: | | ||
| yarn install --frozen-lockfile | ||
| yarn build | ||
|
|
||
| - name: Deploy to ${{ matrix.network }} | ||
| run: | | ||
| cd packages/ethereum-contracts | ||
| npx truffle exec --network ${{ matrix.network }} ops-scripts/deploy-test-environment.js | ||
| npx truffle exec --network ${{ matrix.network }} ops-scripts/info-print-contract-addresses.js : addresses.vars | ||
| tasks/etherscan-verify-framework.sh ${{ matrix.network }} addresses.vars | ||
| env: | ||
| RELEASE_VERSION: canary | ||
| OPTIMISM_SEPOLIA_MNEMONIC: ${{ secrets.BUILD_AGENT_MNEMONIC }} | ||
| OPTIMISM_SEPOLIA_PROVIDER_URL: ${{ secrets.OPTIMISM_SEPOLIA_PROVIDER_URL }} | ||
|
|
||
| publish-release: |
Check warning
Code scanning / CodeQL
Workflow does not contain permissions Medium
Show autofix suggestion
Hide autofix suggestion
Copilot Autofix
AI about 1 month ago
Generally, the fix is to explicitly declare permissions for the workflow or for the specific job, giving the GITHUB_TOKEN the least privilege it needs. For a job that only checks out code and pushes nothing back to GitHub, contents: read is sufficient.
The best targeted fix here is to add a permissions block to the upgrade-contracts job, similar to the one already used in the publish-release job but reduced to only what’s needed. The job steps only read repo contents and use secrets to deploy contracts; they do not push commits, create releases, or modify PRs. Therefore, contents: read is adequate.
Concretely, in .github/workflows/handler.publish-dev-release-packages.yml, under the upgrade-contracts job (around line 289), insert:
permissions:
contents: readbetween the existing if: false # disable this for now and needs: [all-packages-tested]. This change does not alter any behavior besides restricting what the automatically‑provided GITHUB_TOKEN can do when/if the job is enabled.
| @@ -291,6 +291,9 @@ | ||
|
|
||
| if: false # disable this for now | ||
|
|
||
| permissions: | ||
| contents: read | ||
|
|
||
| needs: [all-packages-tested] | ||
|
|
||
| runs-on: ubuntu-22.04 |
There was a problem hiding this comment.
No ops. The default permission is set to read at organization level, this will be a redundant permission. Also, we'd discussed auditing the permissions and application of principle of least privilegesin the workflow, its in the backlogs.
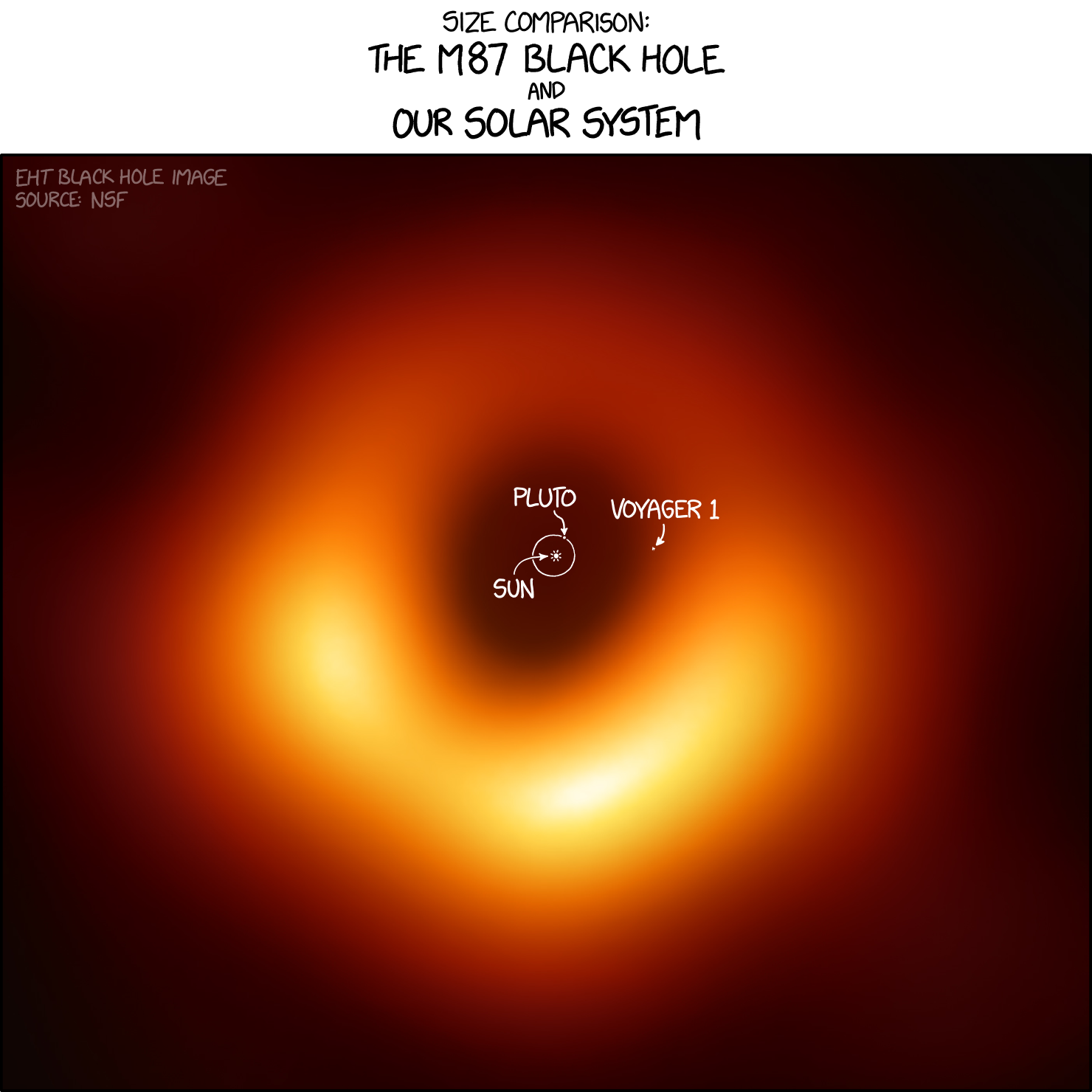
XKCD Comic RelifLink: https://xkcd.com/2135 |
This PR:
ci.canaryandhandler.publish-release-packagesworkflow into onehandler.publish-dev-release-packages. This is to enable trusted publishing of npm packages that requires only one workflow file for package, regardless of if it is dev or released.write-allto a more granular access control.package.jsonto point tosuperfluid-orgas it is a requirement to enable trusted publishing.The configuration needed to enable trusted publishing has been implemented on the NPMJS repository.
Sample of trusted published artefact: https://www.npmjs.com/package/@superfluid-finance/ethereum-contracts/v/1.14.2-dev.dc15170.0